Internet security
made simple
Key benefits
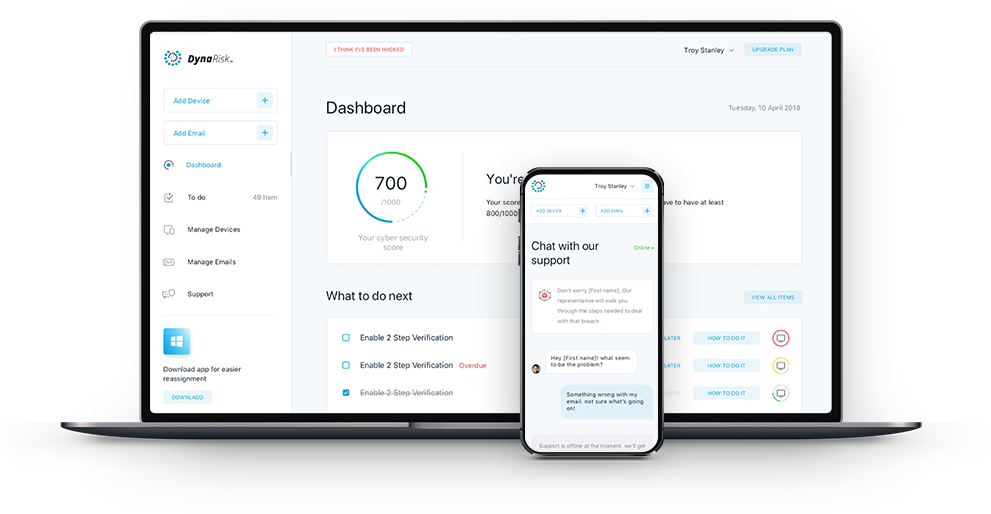
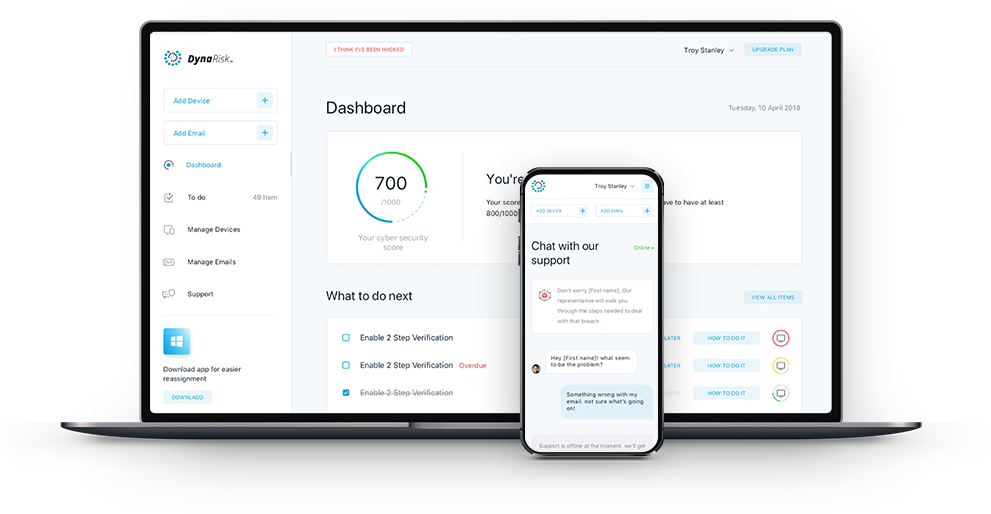
- Cyber Security Score to help you understand exactly how safe you are online and potential areas of risk
- Dashboard containing your Score, reports and recommended actions to help reduce your cyber security risks
- Ability to add and protect family members, securing your home’s entire digital footprint
- Education and threat alerts, direct to your inbox.
Choose a plan
Our plans offer a range of benefits that will help to improve your online safety and your awareness of all things cyber security.
Standard
Basic protection to help keep you safe from common threats.
£19.99
(Billed annually)Advantage
Advanced protection for individuals with a larger digital footprint.
£29.99
(Billed annually)Ultimate
Protect your family and all your devices with our Ultimate home plan.
£49.99
(Billed annually)READ MORE FROM OUR BLOG
Get the latest updates on cyber news, threats and tips to protect yourself, your business and your customers.



